This article describes how to use KisMAC to hack a WiFi password and cautions users to increase their password lengths. First open terminal. We need to know the name of the wireless adapter connected to the computer.
- How To Hack Wifi Password On Mac Using Terminal 2020
- Check Wifi Password Mac
- Hack Wifi Password Using Mac Terminal Software
Step By Step Hack WPA/WPA2 Wi Fi Passwords Using Aircrack Ng
In this tutorial I will tell you how to crack wpa/wpa2 wi-fi in kali linux using aircrack-ng. To do this, first you should install kalinux or you can use live kali linux.
Guys in this tutorial I am going to show you how to get password of saved wifi iilike my video stay updated by subscribing this. Ever thought about getting INFINITE free WiFi at a Hotel, Cruise, Airport or ANYTHING ELSE? Well, me too, and today I'm going to show YOU HOW! Open the terminal window in kali. To open a terminal window in kali use keyboard shortcut ctrl+alt+t.
To crack Wi-Fi, first, you need a computer with kali linux and a wireless card which supports monitor/injection mode. If your wireless card is not able to do this, you need to get an external wireless card which is capable of monitor/injection mode.
Apart from these tools, you need to have a word-list to crack the password from the captured packets.
First you need to understand how Wi-Fi works. Wi-Fi transmits signal in the form of packets in air so we need to capture all the packets in air so we use airodump to dump all the packets in air .After that we should see that if any one is connected to the victim Wi-Fi. If anyone is not connected the Wi-Fi, cracking is not possible as we need a wpa handshake. We can capture handshake by sending deauthentication packets to client connected to Wi-Fi. Aircrack cracks the password.
Step-1:-
First open terminal. We need to know the name of the wireless adapter connected to the computer because computer has many adapters connected.
command for this is : iwconfig
In my case, my wireless adapter is with the name wlan0. In your case, it may be different. If connected to an external wireless card, it may be wlan1or2.
Step-2:-
For some wireless cards, it gives error messages to enable monitor mode on wireless cards. For that, you should use airmon-ng check kill.
Step-3:-
In this step, you need to enable the monitor mode on the wireless card. The command is as follows:
airmon-ng start wlan0 (interface of wireless card).
Now this command will enable the monitor mode on the wifi card. So while using interface in any terminal or command line use wlan0mon.
Note : You should use the interface which is indicated with red mark.
Step-4:-
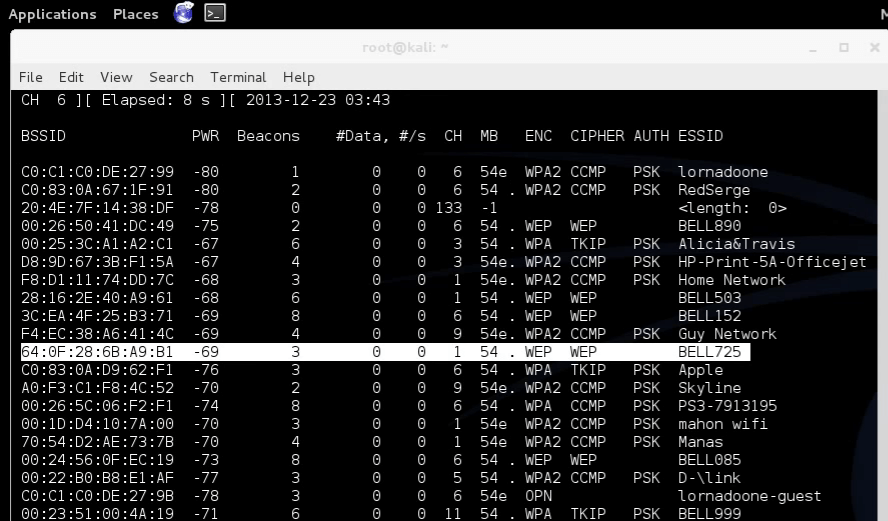
We need to use the command airodump-ng wlan0mon, this will display all the access points in your surroundings and also the clients connected to that access points.
Now this command captures the packets in the air. This will gather data from the wireless packets in the air.
Note : Do not close this terminal. This will be used to know wpa has been captured or not.
Step-5:-
In this step we will add some parameters to airodump-ng.
command is : airodump-ng -c channel –bssid [bssid of wifi] -w [path to write the data of packets] wlan0mon[interface].
- bssid − in my case bssid is indicated with red mark.
- c − channel is the channel of victim wifi in my case it is 10(see in previous screenshot for channel number).
- w − It is used to write the captured data to a specified path in my case it is ‘/root/Desktop/hack’
Interface in my case is wlan0mon.
In the above command the path /root/Desktop/hack hack is the name of the file to be saved.
Above command displays this terminal.
Step-6:-
In this step we deauthenticate the connected clients to the Wi-Fi.
The command is aireplay-ng –deauth 10 -a [router bssid] interface
In the above command it is optional to give the client mac address it is given by
This will disconnects the client from access point.
Screen shot of a client connected to access point.
After this the client tries to connect to the Wi-Fi again. At that time, we will capture the packets which sends from client. From this result, we will get wpa handshake.
Step-7:-
Now we should start cracking the Wi-Fi with captured packets command for this is
path to word list in my case it is ‘/root/Desktop/wordlist.txt’
If you did not have word list, get one. If you want to generate your custom wordlist, you can visit our other post: How generate word list using crunch.
Now press enter aircrack will start cracking the Wi-Fi.
In this article, we will use Aircrack-Ng and dictionary attack method with encrypted password taken from the 4-step handshake process.
When Wi-Fi was first developed in the late 1990s, Wired Equivalent Privacy (WEP) was created to secure wireless communications, but it has many bugs and is easily cracked. For that reason, most wireless access points now use Wi-Fi Protected Access II with pre-shared key for wireless security, also known as WPA2-PSK. WPA2 uses encryption algorithm, AES is stronger, so it is difficult to crack, but not impossible. The weakness in WPA2-PSK system is that the encrypted password is shared during 4-way handshake (4-way handshake). When the client authenticates to the access point (AP), the client and AP perform a 4-way handshake to authenticate the user to the AP. This is the time to hack the password.
- Wireless security: Say NO to WEP and YES to WPA
In this article, we will use Aircrack-Ng and dictionary attack method with the password encrypted from the 4-step handshake process.
- How to find Wi-Fi passwords of relatives
How to hack WiFi password with Aircrack-Ng
Step 1: Set up Wi-Fi adapter in Monitor Mode with Airmon-Ng
First, we need to use a wireless network adapter compatible with Kali Linux.
- The best 8 long-range Wifi routers in 2017
This is similar to setting up a wired adapter in mixed mode (promiscuous mode). It allows to see all the wireless traffic going through. Open the Terminal window and type:
airmon-ng start wlan0
Note, airmon-ng renames adapter wlan0 to mon0.
Step 2 : Get traffic information with Airodump-Ng
Now wireless adapter is in Monitor mode, so all wireless traffic can be seen. Get traffic information using the airodump-ng command.
This command takes all the traffic that the wireless adapter can see and displays important information about it such as BSSID (AP's MAC address), power, beacon frame number, data frame number, channel, speed , encryption (if any), and finally ESSID (SSID). Type the following command in the terminal:
airodump-ng mon0
Note, all visible APs are listed at the top of the screen and the clients are listed at the bottom of the screen.
Step 3: Concentrate Airodump-Ng on an access point on a channel
The next step is to focus on one AP on one channel and collect important data from there. To do this need the BSSID and channel, open another Terminal window and type:
airodump-ng --bssid 08: 86: 30: 74: 22: 76 -c 6 --write WPAcrack mon0
- 08: 86: 30: 74: 22: 76 is the AP's BSSID
- -c 6 is the channel in which the AP is operating
- WPAcrack is the file you want to write
- mon0 is a wireless adapter
As shown in the screenshot above, focus on collecting data from an AP with Belkin276's ESSID on channel 6.
Step 4: Aireplay-Ng Deauth
In order to get encrypted passwords, we need to have an authentic client for the AP. If it is authenticated, we can remove authentication and the system will automatically confirm it, so that the encrypted password can be retrieved. Please open another terminal window and type:
aireplay-ng --deauth 100 -a 08: 86: 30: 74: 22: 76 mon0
- 100 is the number of un-verified frames
- 08: 86: 30: 74: 22: 76 is the AP's BSSID
- mon0 is a wireless adapter
Step 5: The 4-way handshake process
In the previous step, when they re-authenticate the password, airodump-ng will try to retrieve the password during the 4-way handshake. Go back to the terminal window airodump-ng and check to see if it succeeded.
If on the top right line has ' WPA handshake ' written, it means that the process of obtaining the encrypted password was successful.
Step 6: Now we have the encrypted password in the WPAcrack file. Run the file using a password file, here use the default password list named darkcOde. Now, crack the password by opening a terminal and typing:
aircrack-ng WPAcrack-01.cap -w / pentest / passwords / wordlists / darkc0de
- WPAcrack-01.cap is the file name written in the command airodump-ng
- / pentest / passwords / wordlist / darkc0de is the absolute path to the password file
This process can be relatively slow and tedious. Depending on the length of the password list, you may have to wait a few minutes to a few days. When the password is found, it will appear on the screen. Remember, password files are very important. Try the default password file first and if it fails, proceed to a larger and more complete password file.
How To Hack Wifi Password On Mac Using Terminal 2020
Maybe you want to know: How to hack Wifi passwords using Wifiphisher
Check Wifi Password Mac
I wish you all success!